AD FS 2.0 integration
Active Directory Federation Services (AD FS) is a Single Sign-on (SSO) solution created by Microsoft. It enables organizations to collaborate securely across Active Directory domains with other external organizations such as Condeco, by using identity federation.
Before you start
Before configuring your AD FS integration with Condeco, Condeco must create an IdP connection and provide you with the associated metadata to import when creating the relying party trust. To create the IdP connection, Condeco first needs your metadata:
- Get your metadata: Your metadata can be found here: https://[Your server name or public URL]/FederationMetadata/2007-06/FederationMetadata.xml
- Send metadata to Condeco : Save your metadata and send it to Condeco via your agreed method.
When we have received your metadata file and created the IdP connection, we will provide you with the associated metadata to use for the integration. When received, follow the steps below to integrate AD FS 2.0 with Condeco.
Process overview
- Add a relying party (RP) trust to AD FS.
- Add the claims rules.
- Map LDAP attributes to the outgoing claims rules.
Prerequisites
- A metadata XML file provided by Condeco (see ‘Before you start’ for more information about the metadata file).
How to integrate AD FS 2.0 with Condeco
Follow the steps below on the federation server to integrate AD FS 2.0 with Condeco.
Add a relying party trust to AD FS
A relying party (RP) trust is a trust object created to maintain the relationship with a Federation Service or application that consumes claims from the Federation Service.
To add a new relying party trust, use the AD FS Management snap-in and manually configure the settings. Follow the steps below on the federation server.
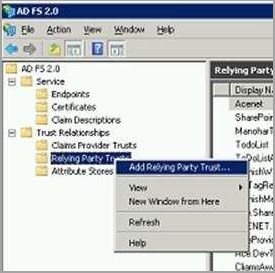
- Launch AD FS 2.0 Management from the federation server.
- Navigate to Trust Relationships > Relying Party Trusts.

- Right-click Relying Party Trusts (or click Action from the menu bar) and select Add Relying Party Trust… to start the wizard.
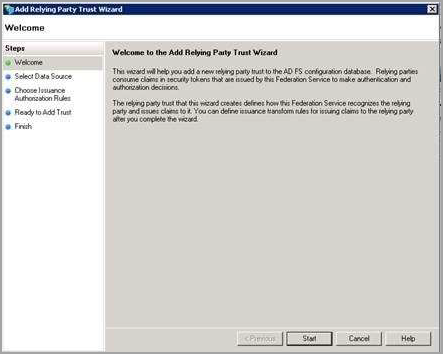
- When the Add Relying Party Trust Wizard opens, click Start.
- Select Import data about the relying party from a file and enter the path to the metadata provided by Condeco. Click Next.
- Enter a name for the relying party trust (for example, “Condeco SSO”) in the Display name field and click Next.
- Select I do not want to configure multi-factor authentication settings for the relying party trust at this time and click Next.
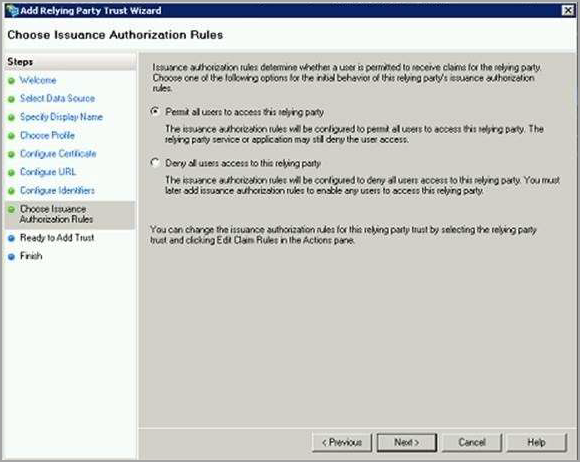
- Select Permit all users to access this relying party on the Choose Issuance Authorization Rules page and click Next.
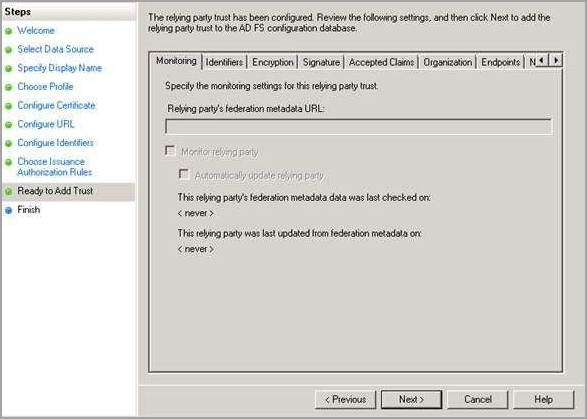
- The relying party trust is now configured. Click Next to launch the Claim rules.
Adding claim rules
The primary function of the Federation Service in AD FS is to issue a token containing a set of claims. Claims rules govern the decision in regard of claims that AD FS issues. Claim rules and all server configuration data are stored in the AD FS configuration database.
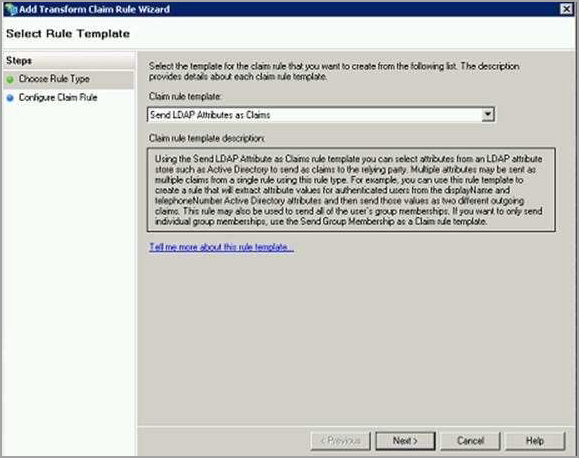
- From the Edit Claims Rules for …. Relying Party window, click Add Rule..

- Select Rule Template: Select Send LDAP Attributes as Claims from the Claim rule template drop-down list.
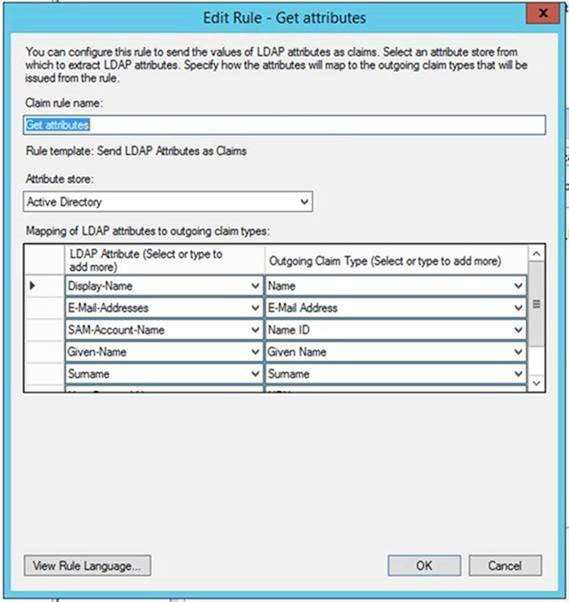
- Configure Rule: Enter a name for the claim rule in the Claim rule name field and select Active Directory from the Attribute store drop-down list. Now you can map LDAP attributes to outgoing claim types.
Map LDAP attributes to outgoing claim types
- Map the following LDAP attributes to the outgoing claim types:
| LDAP Attribute | Outgoing Claim Type | More information |
|---|---|---|
| Display-name | Name | |
| E-Mail-Addresses | E-Mail Address | |
| SAM-Account-Name | Name ID | Condeco recommend using SAM-Account-Name for consistency. |
| Given-Name | Given Name | |
| Surname | Surname |
- When all required claims are mapped, click OK to close the wizard.
What’s next?
When the metadata has been exchanged you are ready to test the connection via your Condeco website URL.
We highly recommend creating an AD FS test account for Condeco to assist you with the connection testing.
