Security Roles and Roles Management
Level: Administrator
Security Roles determine what the user can see and do in Eptura Asset. Your Administrator has the ability to add new roles and the default roles are:
- Administrator
- Full User
- No Access
- Read Only
This article contains:
- Access Security Roles
- Add a New Role
- Define the Role's Module Access
- Grant Module Access
- Turn Full Administration Access ON vs granting specific Module Access
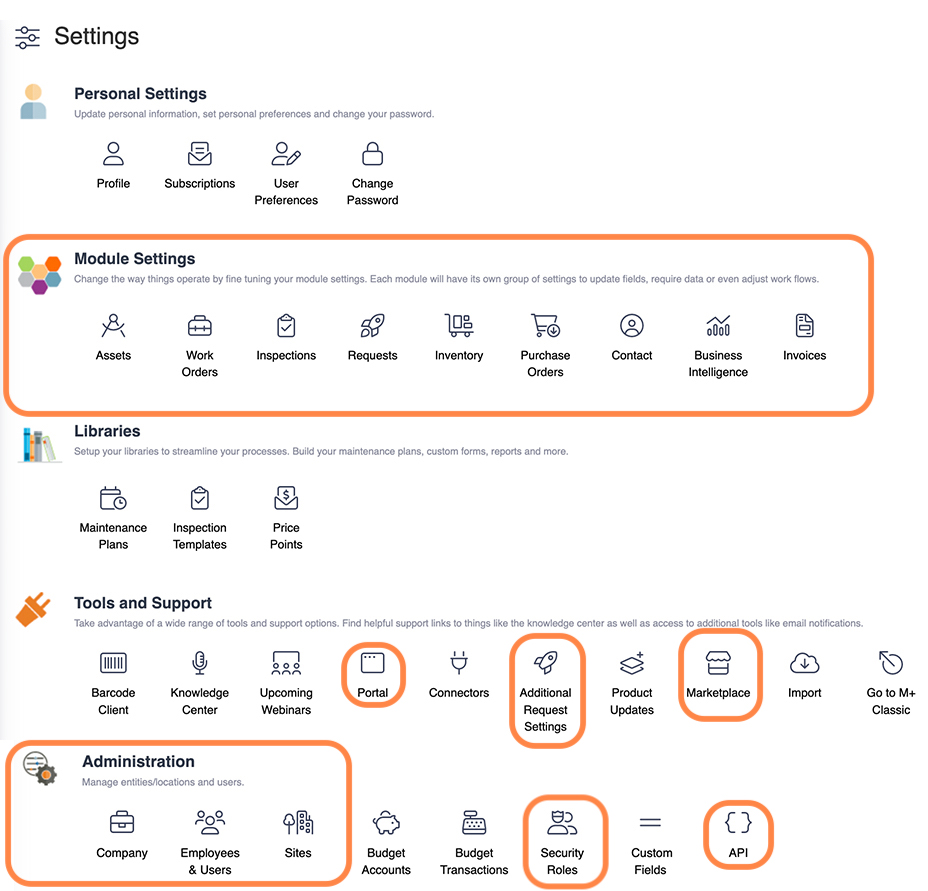
Access Security Roles
- From the menu, click Settings.
- Under the Administration section, click Security Roles and the Roles Management screen displays.
Your Administrator will create roles and define the modules access this will help with:
- Administrators - When you limit access to the configuration and settings this prevents well-intentioned users from changing settings or configuration for others.
- Inventory quantities - When you only allow certain roles to update or change inventory quantities, this helps to protect the integrity of your inventory numbers.
- Technician and Operators - When you have many technicians or operator then these users can be in the same group you will know what they can see and what they can access.
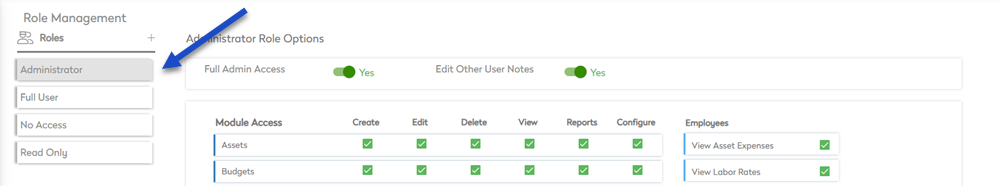
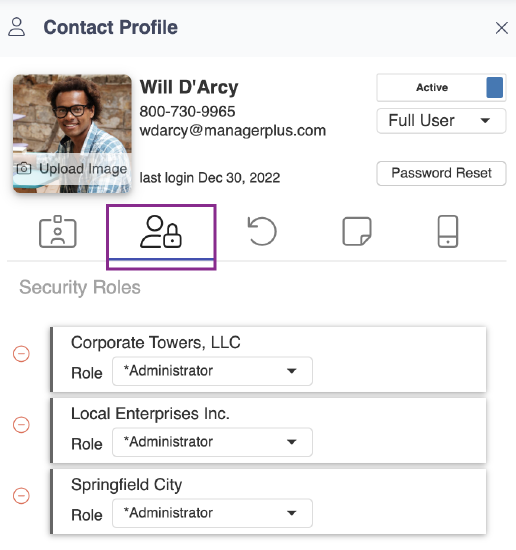
In this example, the user is set up as an Administrator.
Add a New Role
You can create additional roles.
- Click the + icon.
The Add New Role dialog displays.
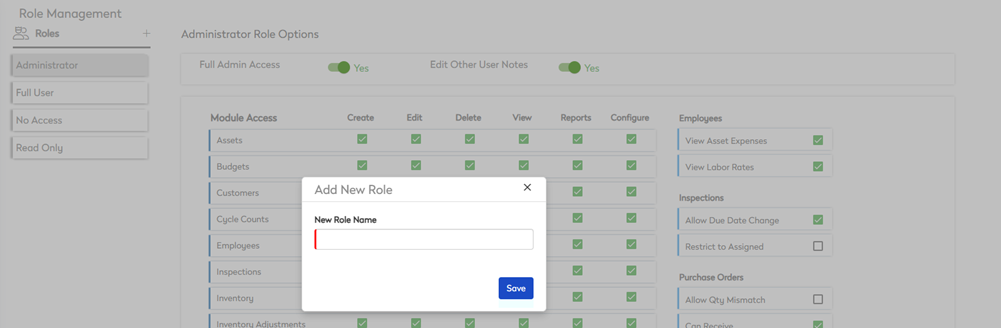
- In the New Role Name field, enter the name of the role.
- Click the Save button.
After the role has been created, then you can define the role's module access.
Define the Role's Module Access
After the role has been created, then you can define the role's
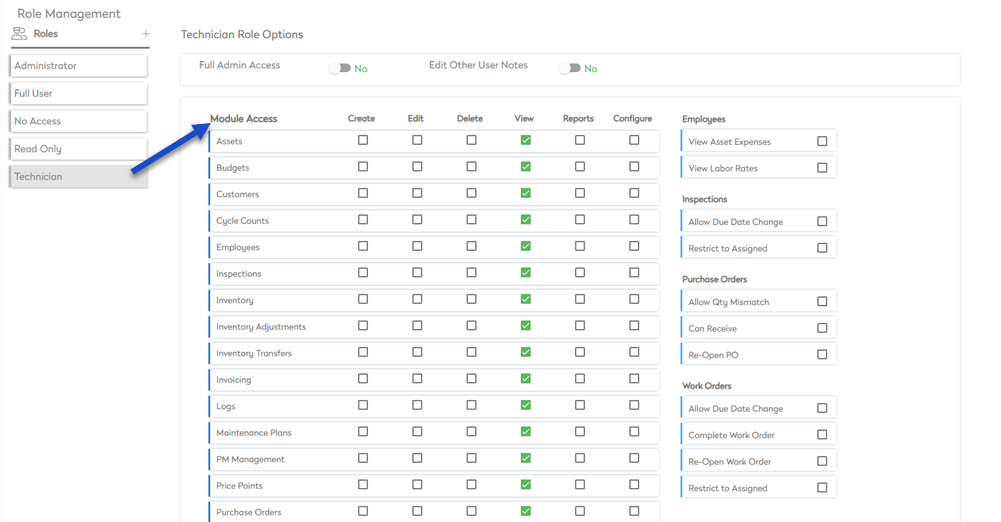
By default, the Administrator role is the only one to give you access to all six main Module permissions:
- Create - Allows the user to create a new record that did not exist previously.
- Edit - With this permission, the user can add or alter documentation to an existing record (including change names, correct errors, add notes, change ID's, etc).
- Delete - The record can be deleted entirely, with no possibility of recovery. Even if you have Delete rights, most modules will block you from deleting a record, if that record has any recorded history on it. This includes: Assets, Budgets, Employees, Inventory, PMs, Users, and Vendors.
- View - The user can view any/all of the details of that module. Unless they have additional rights granted, this is all they can do inside the selected module.
- Reports - The user can run any of the reports of the selected module.
- Configure - This grants the user permission to change the settings of the selected module, and amend what options all other users will be able to see in the module.
Grant Module Access
On the right side of the screen, you will notice security settings that are unique for specific modules.
Let's clarify a few of these:
- Employees
- View Labor Rates - User and employees can see labor rates on Work Orders.
- Inspections
- Restrict to Assigned - When turned ON, the user can ONLY see Inspections assigned to them.
- Purchase Orders
- Allow Qty Mismatch - This allows the purchase order to receive a different amount than was ordered. If you ordered 3 and only received 2, this allows the user to close the purchase order.
- Work Orders
- Restrict to Assigned - When turned ON, the user can ONLY see Work Orders assigned to them.
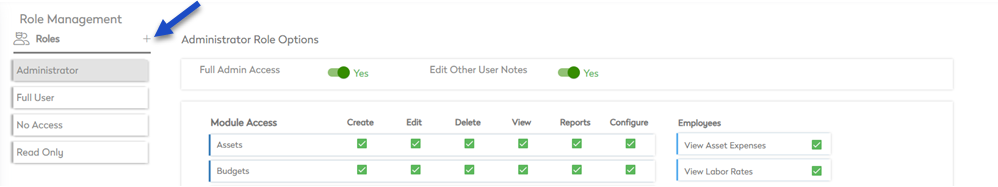
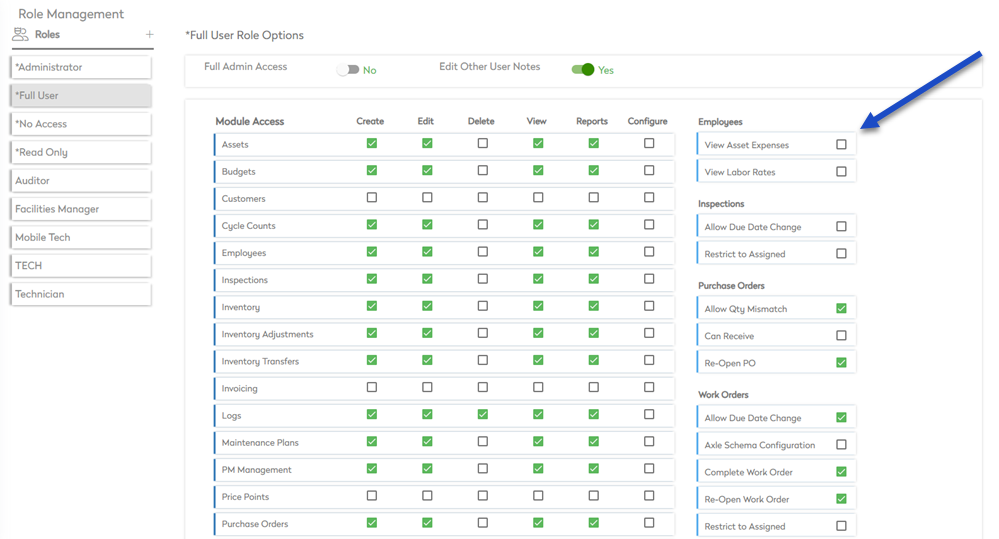
Turn Full Administration Access ON vs granting specific Module Access
When the Full Admin Access toggle is ON at the top of the screen then access to all the Module Settings is granted. It is NOT the same as manually granting the user Configure rights on all modules. It simply allows the user permission to open and view the module settings and the configure rights are still needed to make changes.
Full Admin Access is NOT necessary if the user only requires Configure rights to one or more modules. However, if they will also need control of Administration Tools, or global settings (such as Company addresses, Inventory warehouse setup, Asset Group/Location setup, etc.), Full Admin Access will be required.
Full Admin Access will also grant you viewing access to these tools & administration areas on the Settings Page shown below: